How to collect a Wireshark network capture
The article was successfully sent to the email
About
Information from Official Wireshark site:"Wireshark is the world’s foremost and widely-used network protocol analyzer. It lets you see what’s happening on your network at a microscopic level and is the de facto (and often de jure) standard across many commercial and non-profit enterprises, government agencies, and educational institutions. Wireshark development thrives thanks to the volunteer contributions of networking experts around the globe and is the continuation of a project started by Gerald Combs in 1998."
As Motorola DMR and TRBOnet software are heavily TCP\IP dependent, Wireshark allows to analyze traffic which comes to or from TRBOnet computer.
Installation
Wireshark can be downloaded from official Wireshark site -> Downloads sectionDownload appropriate architecture version (x86 or x64), depending on Windows architecture installed.
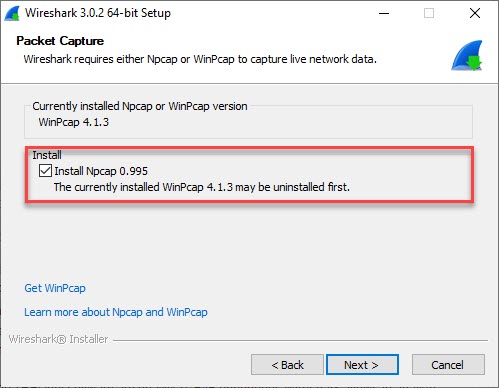
Always allow to install WinPcap or Npcap (depending on Wireshark version) drivers, it allows Wireshark to detect Network interfaces of Computer.
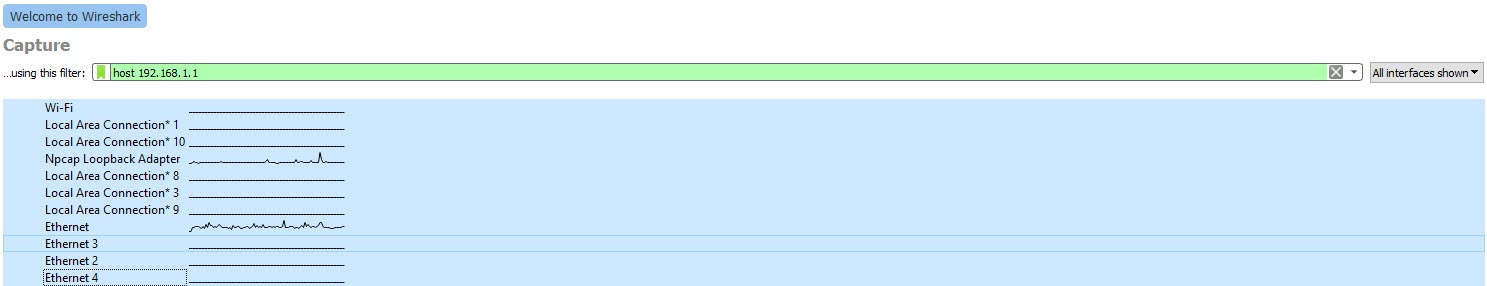
After Wireshark start, make sure Network interfaces appeared in list of Interfaces (Example, list of actual interfaces on target computer may vary):
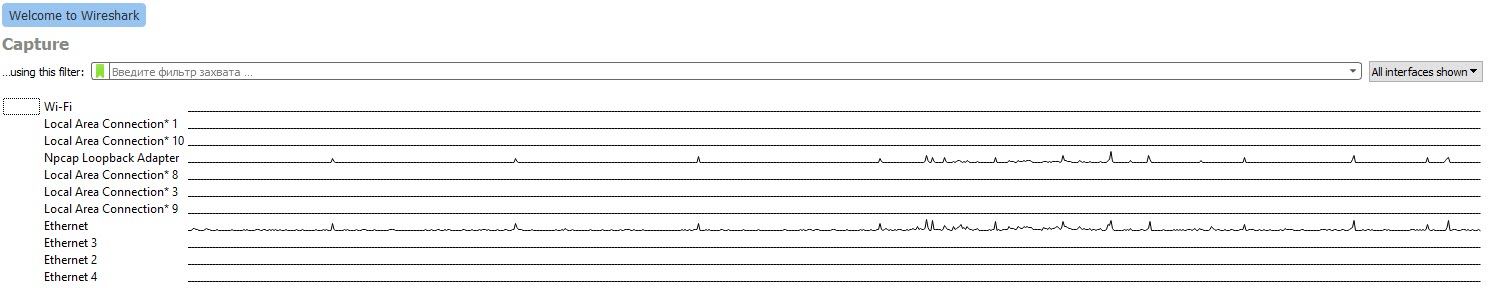
If no Interfaces appear, try to start Wireshark using Administrator privileges if this didn't help, try to restart computer.
Capturing
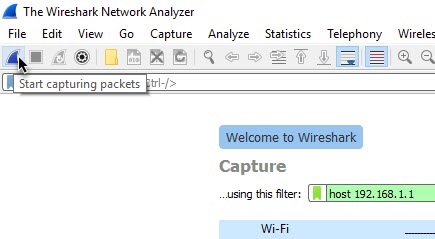
To provide requested logs, choose all available Network Interfaces holding Shift (highlight changes to blue).After Interfaces are set, start Wireshark log to capture behavior for analysis:
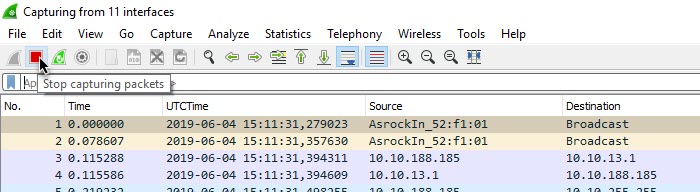
To stop Capturing click on Stop button:
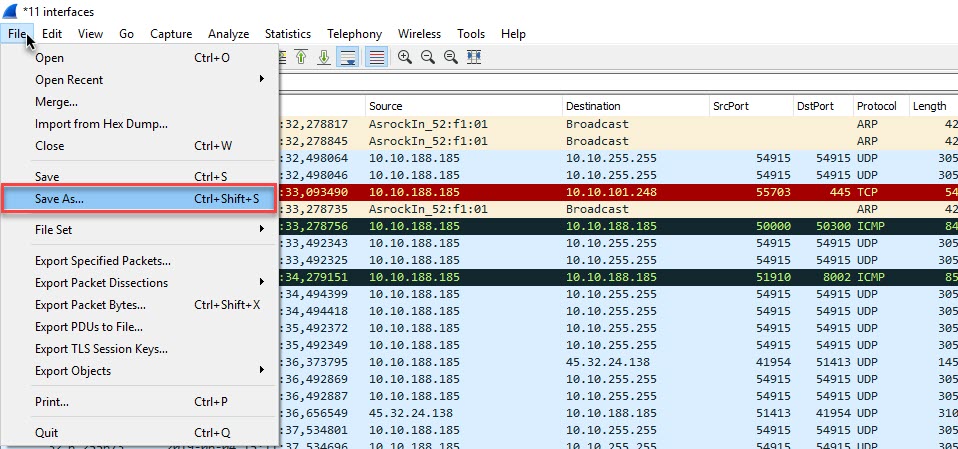
Save captured log:
Save options
If Behavior appears through long period or unstable and can't be reproduced right away, it might be required to start Wireshark log gathering for a longer period.As, by default, Wireshark saves log to RAM, to avoid RAM over-consumption, configure saving file on disk.
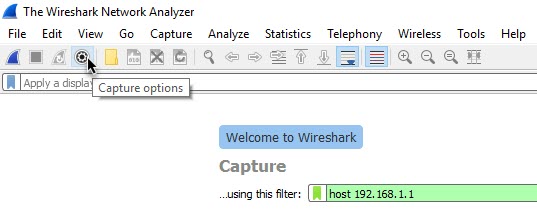
Go to Capture options:
Output, and choose path to save log file.
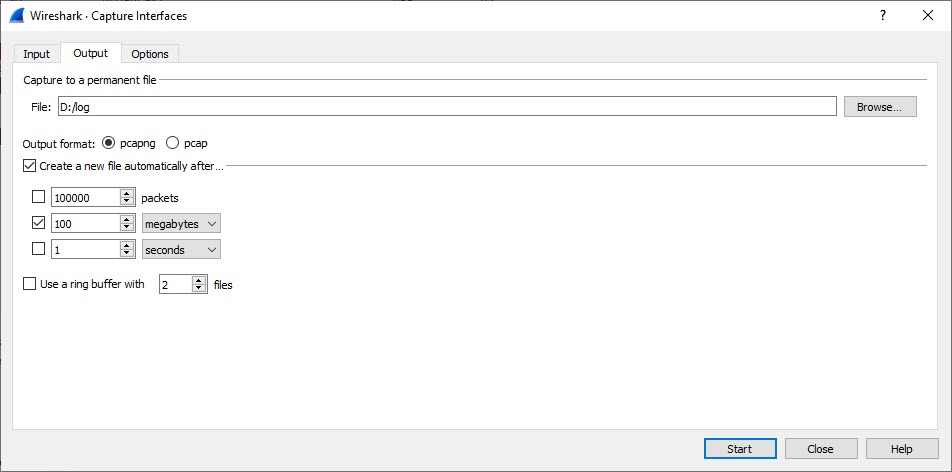
Additionally it is possible to set Wireshark to create new file each specified Time period or Packets amount captured etc., for example, Wireshark will create new file each 100 megabytes of information:
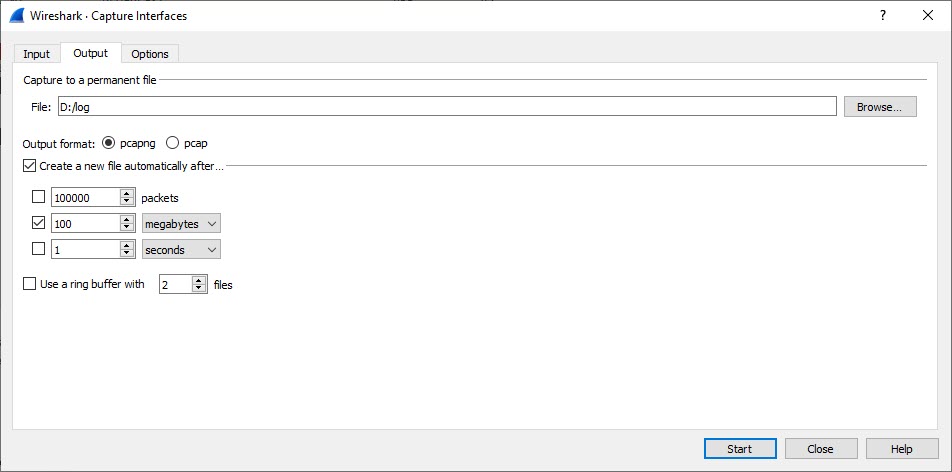
It is also possible to set different filters to capture only required information to minimize log size..
For example, in capture filter use syntax "host" (without quotes) and IP address required for capture, Example: host 192.168.1.1. Now log will capture only packets with Source or Destination ip address 192.168.1.1:
Other filter options also available and can be found on Wireshark Wiki site -> Capture Filters